One of the many things you can use a Mikrotik router for is to deny users access to websites like Facebook, YouTube and all adult websites during working hours. By doing this, you save your organization appreciable amount of bandwidth for legitimate traffics such as email, Skype calls, hotel reservations, online biddings, just to mention but a few. But what happens when a configuration mistake allows users to circumvent your policies and have access to these websites? In this demonstration, I will share with us on how a user can bypass Mikrotik layer 7 filtering and have access to blocked websites as a result of a harmless mistake from a network administrator.
I have made several posts on how to block websites using Mikrotik routers but for the sake of this post, I will be working us through the creation of a Mikrotik layer 7 rule to block websites, point out the mistake that can allow users gain access to these blocked sites via VPN, and finally show us how to ensure users do not have the last laugh.
There are basically two things to do when trying to block access to some websites on a Mikrotik router: create a layer 7 protocol with all websites to be blocked listed, and configure a firewall deny rule that will make use of the layer 7 protocol. The harmless mistake is usually in the firewall rule. I call it harmless because everything works well until a smart user gets connected to your network.
Creating Mikrotik layer 7 protocol
To create the layer 7 protocol, we go to ip >> firewall >> layer and enter the codes as shown in the image below:

Creating a Mikrotik firewall filter rule
Next, we configure the firewall filter rule to make use of the layer7 protocol above. To do this, we go to IP >> firwall >> filter and add the rules as shown in the image below. Watch out for that mistake. See below:

Click on action and choose drop.
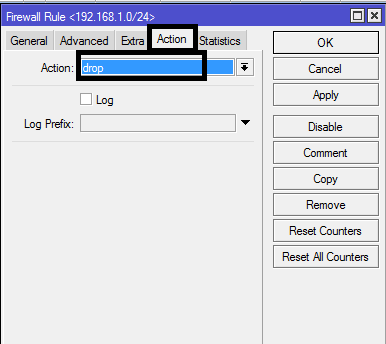
Or simply enter the following codes: /ip firewall filter add chain=forward src-address=192.168.1.0/24 layer7-protocol=xxx action drop
The rule above will block websites based on source IP address. As long as a user’s IP is within the 192.168.1.0/24 subnet, that user will not have access to the websites listed in the layer 7 protocol. Okay, it makes sense now. But what happens when a user decides to use VPN? Yea, VPN. There are lots of free VPN on the net. A user can easily download any of them and run it and his/her source IP changes to something else. What happens then? I tried this and had unrestricted access to the blocked sites when using VPN (VPN Matser).
You may also like: how to permit only company-allowed websites on Mikrotik
The harmless mistake
Denying users access to some websites on Mikrotik does not just end with configuraing a firwall filter rule and a layer 7 protocol as shown above, except you trust your users not to be smart enough to download one of the hundreds of free vpn available online. This is where most network administrators get it wrong. You need to configure more firewall filter rules to ensure that users do not use vpn to bypass the rules created above.
Creating rules that block the use of vpn on Mikrotik routers.
We will create more firewall filter rules to block the following protocols: ipsec-esp, ipsec-ah, gre, and ipip
/ip firewall filter
add chain=forward protocol=50(ipsec-esp) out-interface=ether1 action=drop
add chain=forward protocol=51(ipsec-ah) out-interface=ether1 action=drop
add chain=forward protocol=47(gre) out-interface=ether1 action=drop
add chain=forward protocol=94(ipip) out-interface=ether1 action=drop

Once this is done, vpn connections initiated from within your network will be denied. The third rule did it for me; that’s the rule that blocked the use of VPN (VPN master) on my network and ensured I had no access to blocked network resources through the use of VPN.
To have my posts sent directly to you via emai, kindly subscibe to this blog by clicking on the subscribe button and also subcribe to my Youtube channel, like my Facebook page and follow on Twitter.
For more on Mikrotik firewall filter rules, please visit wiki.mikrotik.com

disable only on LAN cable enable through wifi
Hi,
I followed all the steps to avoid the bypass but some of my users are using an android app called SuperVPN, and with the rules that I create based on your post, they do not block access to those apps, could you help me?