Wrong username or password displayed when trying to access a Mikrotik router could mean your login credentials have been entered wrongly or your Mikrotik router has been compromised. In this post, we are concerned with what happens when the latter occurs.
Users of Mikrotik routerOS have experienced unprecedented attacks recently. Many of my readers have complained about seeing ‘wrong username or password’ displayed when trying to access their routers via the WAN port. These same users are able to access same routers from the LAN using the same login credentials. What then could be wrong? If you are reading this post and you are experiencing same issue on your mikrotik router, your device has been hacked!
What they do to affected Mikrotik routers
The hackers will configure access-class filters on hacked devices to permit a few source IPs from accessing the router. In the filter, they include the LAN subnets configured on the router and a host of their (attackers’) IP addresses. Users who try to access the affected router using source IPs not listed in the access-class will see the ‘wrong username of password’ message displayed.
When trying to access your router from outside your network, using the public IP configured on the router, access will be denied and a message saying ‘wrong username or password’ will be displayed. This happens because your source IP is not listed in the access-class configured by the hackers.
How to resolve Mikrotik wrong username or password issue
If you can access the router from within your internal network, follow the steps below to resolve the issues otherwise, I recommend you reset the router.
Step 1: Change username and password
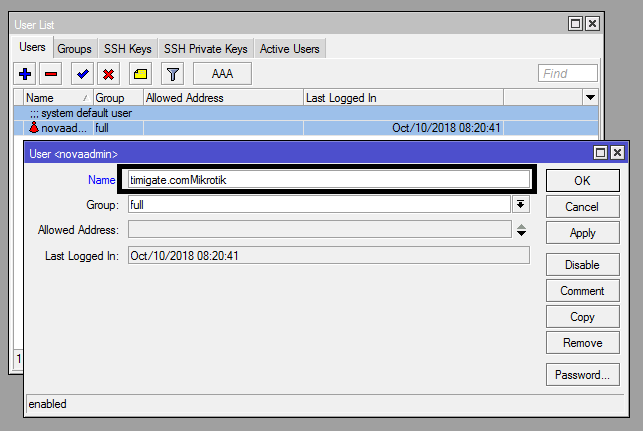
Change all configured usernames and passwords on the router. Click on system>users. Select a user and change the name.
After changing your username on the Mikrotik router, logout of the router and login with the new username and old password. Click on system>password to set a new password.
Step 2: Remove configured source IPs from access-class
Once logged into your router from the internal network, click on IP>Users to see all configured users on the router. If you find any user not configured by you, remove it. Then, double on all configured users, including the admin and remove all source IPs configured by the attackers. Having no source IPs configured on users means device can be accessed from any IP as long as the correct username and password are entered.
If you want to limit remote login to a known IP used by you, enter such IP alone in the allowed address field.

Step 3: Update routerOS
Mikrotik is usually aware of bug in routerOs that hackers leverage on to have unauthorized access to devices on the internet. In response, they create fixes that are pushed out to devices via system updates. System updates are highly recommended to Mikrotik users with devices on the internet.
To update your router, click on system>packages>Check for updates. If your router is unable to resolve hostname, it means you do not have a functional dns server address assigned. Click on IP>dns and assign a dns IP (8.8.8.8) to your router. After that, go back and check for updates. Click on download and install update. The router will download and install system updates on your router.
Read: How to remove Mikrotik router ports from slave mode
Step 4: Remove scripts and schedulers created by hackers.
The attackers often create scripts on affected routers. The scripts, among other things, will reboot your router, change the admin password, and install files in the file menu of your router. Click on system>scripts and remove these scripts.

Because they want the scripts to continue running without human intervention, thy will automate the scripts’ execution using system schedulers. Click on system scheduler and remove all schedulers not configured by you.

How to protect the router from further attacks
After cleaning up your router, you will need to protect it from further attacks by disabling access to the router from the internet on selected ports. Access an be granted for selected IP addresses. Read: How to secure Mikrotik routers by blocking port access from the internet
If you enjoyed this tutorial, please subscribe to this blog to receive my posts via email. Also subscibe to my YouTube channel, like my Facebook page and follow me on Twitter.
